The iPhone has a serious issue that can affect any of its 1 billion users, potentially leading to catastrophic consequences if targeted. Unfortunately, Apple appears to be either hesitant or incapable of addressing this problem. This guide aims to outline the issue and provide you with 11 practical tips to safeguard yourself.
- What is the Problem?
- 11 Tips to Protect Your iPhone from Hackers
- 1. Use Strong Passcode
- 2. Always try to use Biometrics
- 3. Use a Third-Party Password Manager
- 4. Phishing Attacks
- 5. Avoid Free Wi-Fi & Charging Stations
- 6. Software Updates
- 7. Turn on "Block Pop-ups"
- 8. Turn on "Prevent Cross-Site Tracking"
- 9. Turn on "Fraudulent Website Warning"
- 10. Security Recommendations
- 11. 2-Factor Authentication
What is the Problem?
Recently, the Wall Street Journal published a story about Reyhan Ayas, a woman from New York who had her iPhone stolen as she was leaving a bar in Manhattan. Although iPhone theft is not an uncommon occurrence, what happened next was unusual. Within a short time after the theft, Ayas found herself locked out of her iCloud account on all of her connected devices, including her MacBook at home. As a result, the thieves were able to move approximately $10,000 from her bank account to theirs in just a few hours.
You can watch the full story on youtube, but let me give you a really quick summary of what happened.
Before the theft, Reyhan had a conversation with a man at the bar, during which she unlocked her iPhone by entering her 4-digit passcode, instead of using Face ID or Touch ID. This made her a target for the thieves who stole her phone, and ultimately caused her to be locked out of her iCloud account. The issue with passcodes is a common problem with iPhones, as they can be easily cracked with the right tools and knowledge, making it important for users to use stronger authentication methods like biometrics or longer, more complex passcodes.
The police suspect that while Reyhan was talking to the man at the bar, there may have been someone else working with him, possibly tasked with observing her as she entered her passcode. A 4-digit passcode is relatively easy to see if someone is close enough to watch it being entered, especially if it’s a simple and memorable one. The subsequent theft of her phone was a straightforward process – wait until she was leaving the bar, grab the phone from her hand, and then use the passcode to access her iCloud account and steal money from her bank account. This incident highlights the importance of being aware of your surroundings and taking necessary precautions to protect personal information, including using stronger passcodes and avoiding using them in public places where they may be observed.
11 Tips to Protect Your iPhone from Hackers
Now, assuming nothing happens to you, but still I am going to give you 10 tips that you can follow to protect your phone from hackers, and even if your phone is stolen, the hacker will not be able to do anything.
1. Use Strong Passcode
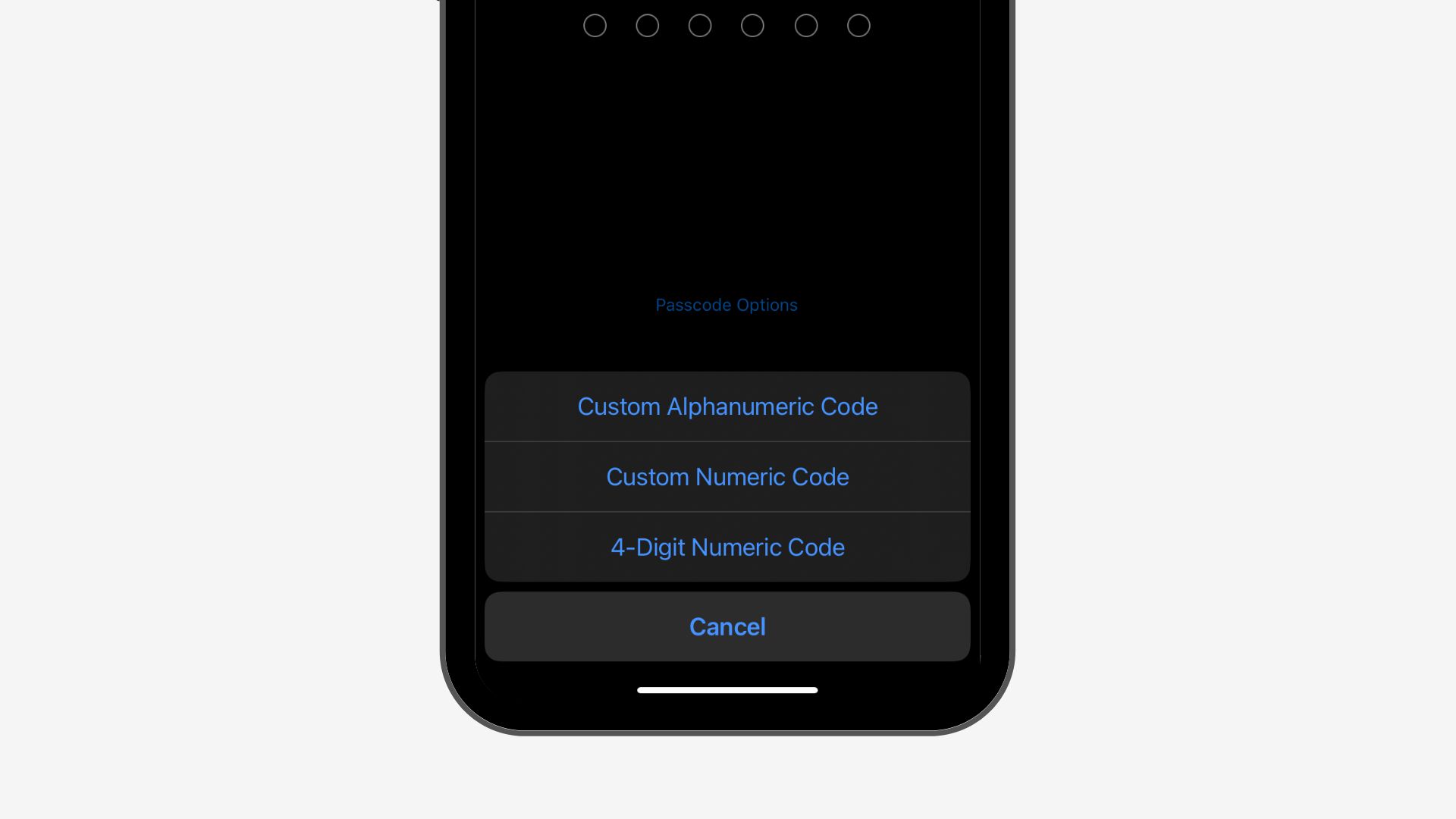
It’s important to use a strong alphanumeric passcode to ensure the security of your device. To do this, you can go to Settings and select FaceID and Passcode. Then, choose Change Passcode and select Passcode Options to choose a custom alphanumeric code, a custom numeric code, or a 4 digit code. While a 4-digit code may be convenient, it’s also easy for someone else to remember, making it less secure. A 6-digit numeric code is better, while a 6-digit alphanumeric or a 10-digit alphanumeric code would provide even stronger security.
2. Always try to use Biometrics
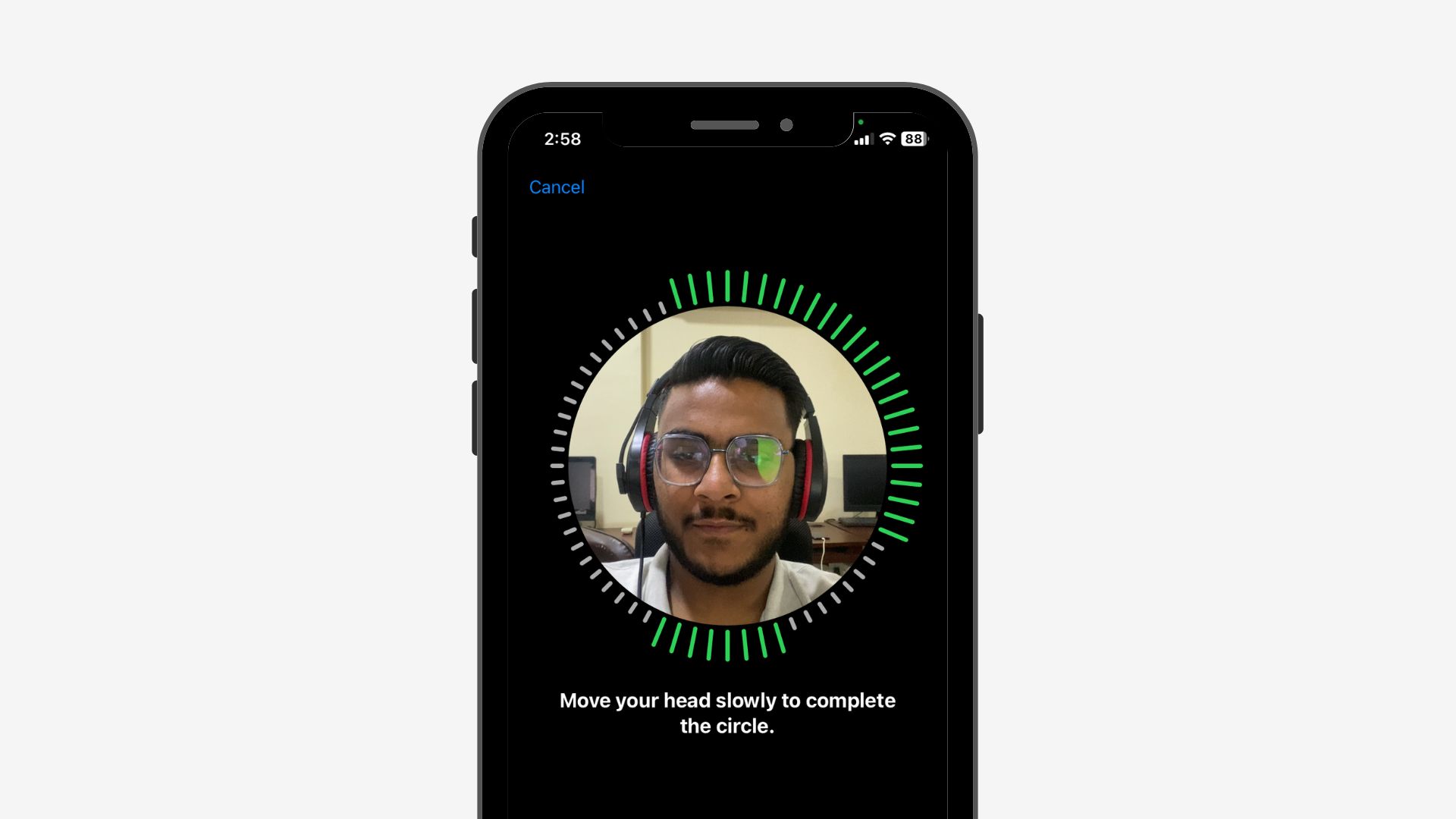
There are individuals who choose not to utilize Touch ID or Face ID due to various reasons such as mistrust of the technology or Apple, suspicion of the collaboration between Apple and the Illuminati, or simply a personal preference against using them. However, it is important to note that biometric authentication is significantly more secure than traditional passcodes.
3. Use a Third-Party Password Manager
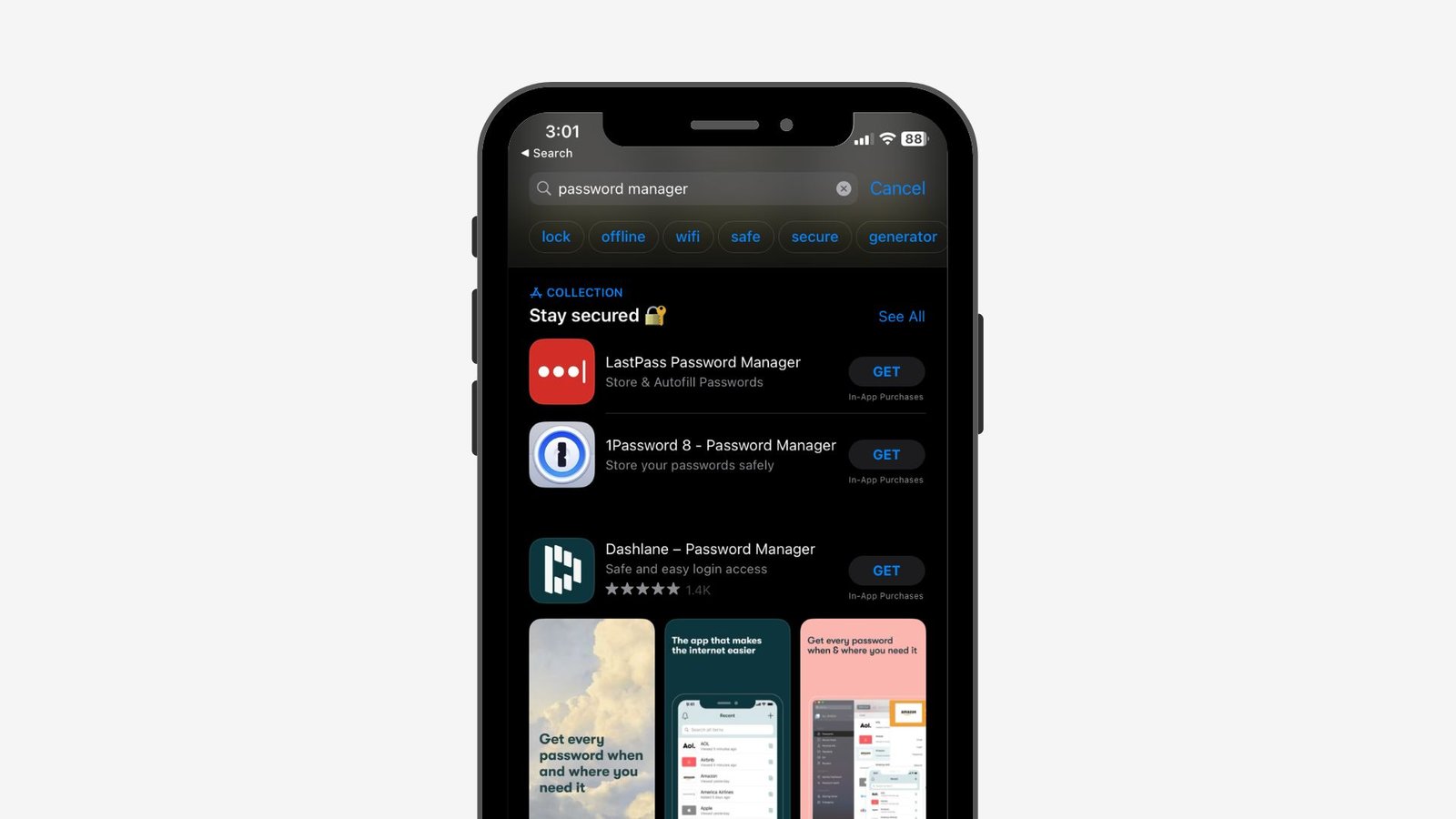
Although I’m an avid user of Apple products and rely on iCloud Keychain for storing my passwords on my iPhone, Mac, and iPad, I must admit that there is a potential security risk associated with it, as discussed in this guide.
Despite my confidence in using Face ID and a strong passcode to protect my phone, I’m aware that if someone gained access to my phone and passcode, it could compromise the security of all my stored passwords. To mitigate this risk, I suggest considering a third-party password manager that offers a separate password to access the manager. This additional layer of security would prevent unauthorized access to my stored passwords in case someone were to access my phone.
4. Phishing Attacks
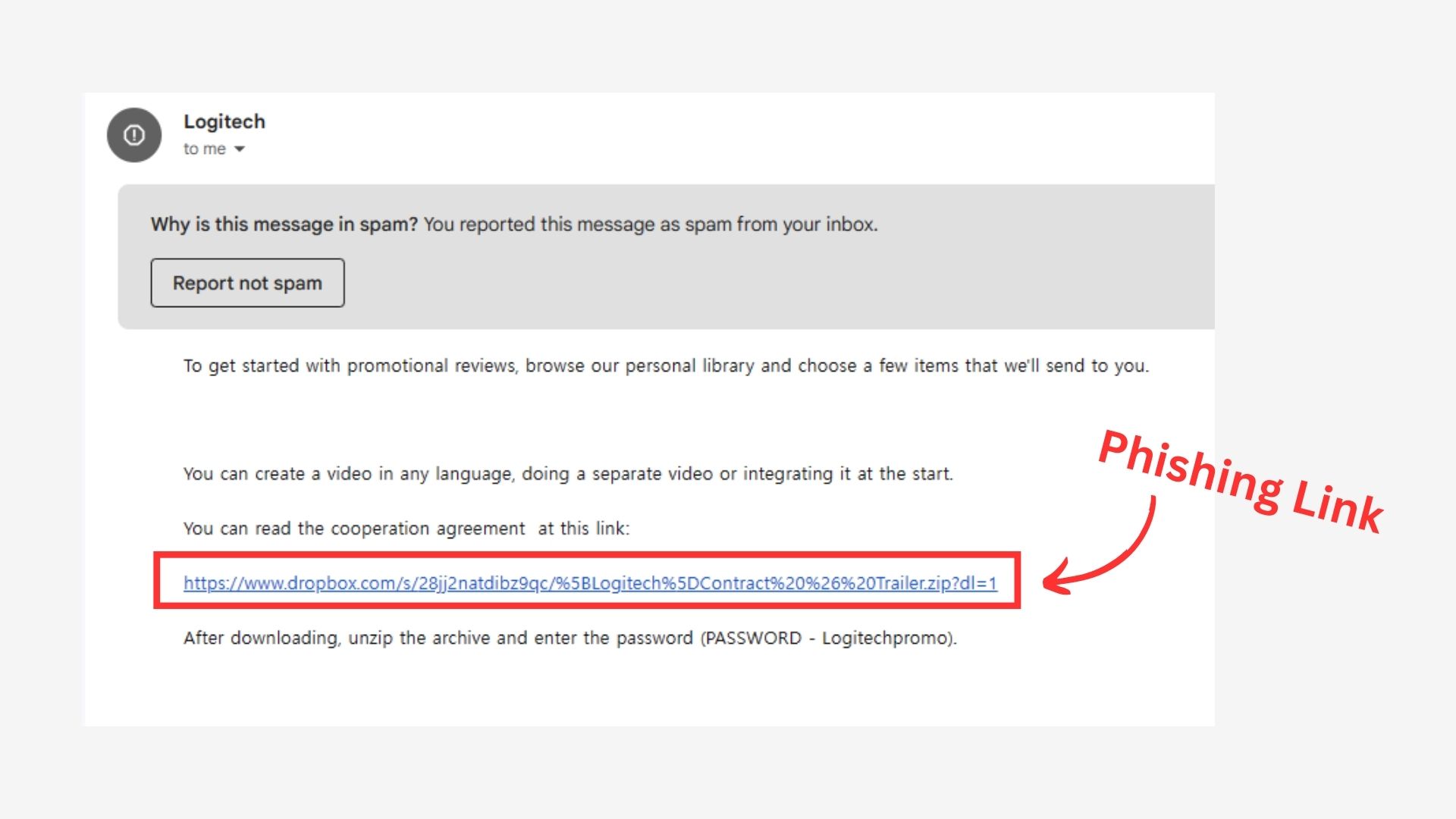
It’s essential to be mindful of emails and messages claiming we’ve won an Amazon sale or someone accessed our Instagram account. Clicking on these can install malware and compromise our device’s security, allowing cybercriminals to spy on us or steal data. Stay vigilant and avoid clicking on links or downloading attachments from unverified sources to protect your digital identity.
5. Avoid Free Wi-Fi & Charging Stations

While public Wi-Fi and charging stations may seem like convenient amenities, they can also pose significant security risks to our devices and personal data. To safeguard against potential threats, it is crucial to avoid connecting to sketchy networks whenever possible.
If you must use public Wi-Fi, be cautious when performing sensitive activities such as banking transactions and consider using a virtual private network (VPN) for added security. Additionally, carrying your own charger or power bank can help reduce the need to rely on potentially unsafe charging stations.
Remember, while free Wi-Fi and charging may be tempting, the potential consequences of exposing your personal information and compromising your device’s security are not worth the risk. By taking these simple precautions, you can help protect yourself against cyber threats while on the go.
6. Software Updates
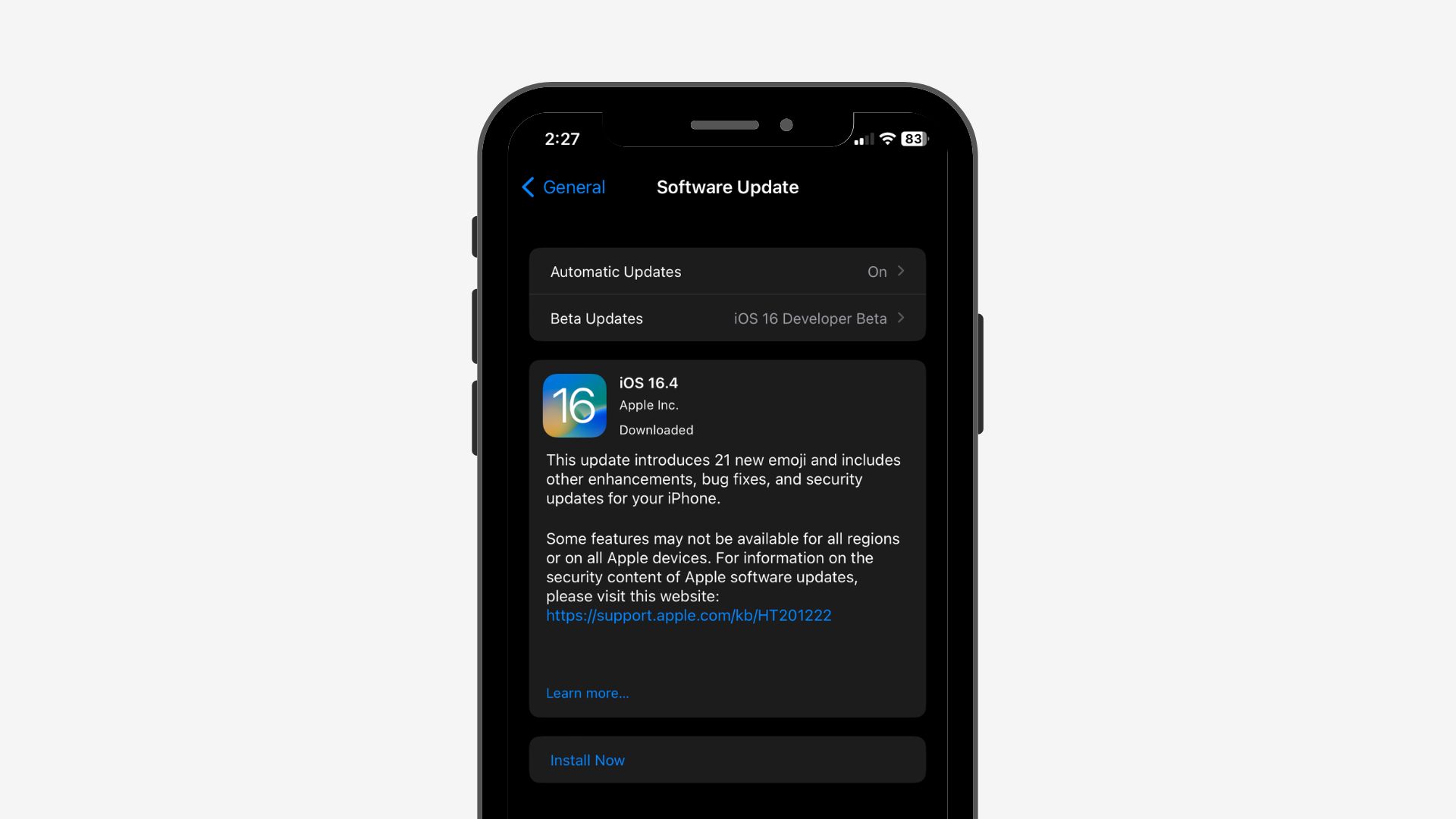
Another essential step to protect your online security is to regularly download and install software updates. While it’s advisable to wait a short while before installing new updates, it’s also important not to procrastinate or avoid them for an extended period. Some updates include critical security patches for newly discovered vulnerabilities, making them essential to protect your devices from potential cyber-attacks. By keeping your software up to date, you can help safeguard your personal information and keep your devices secure.
7. Turn on “Block Pop-ups“
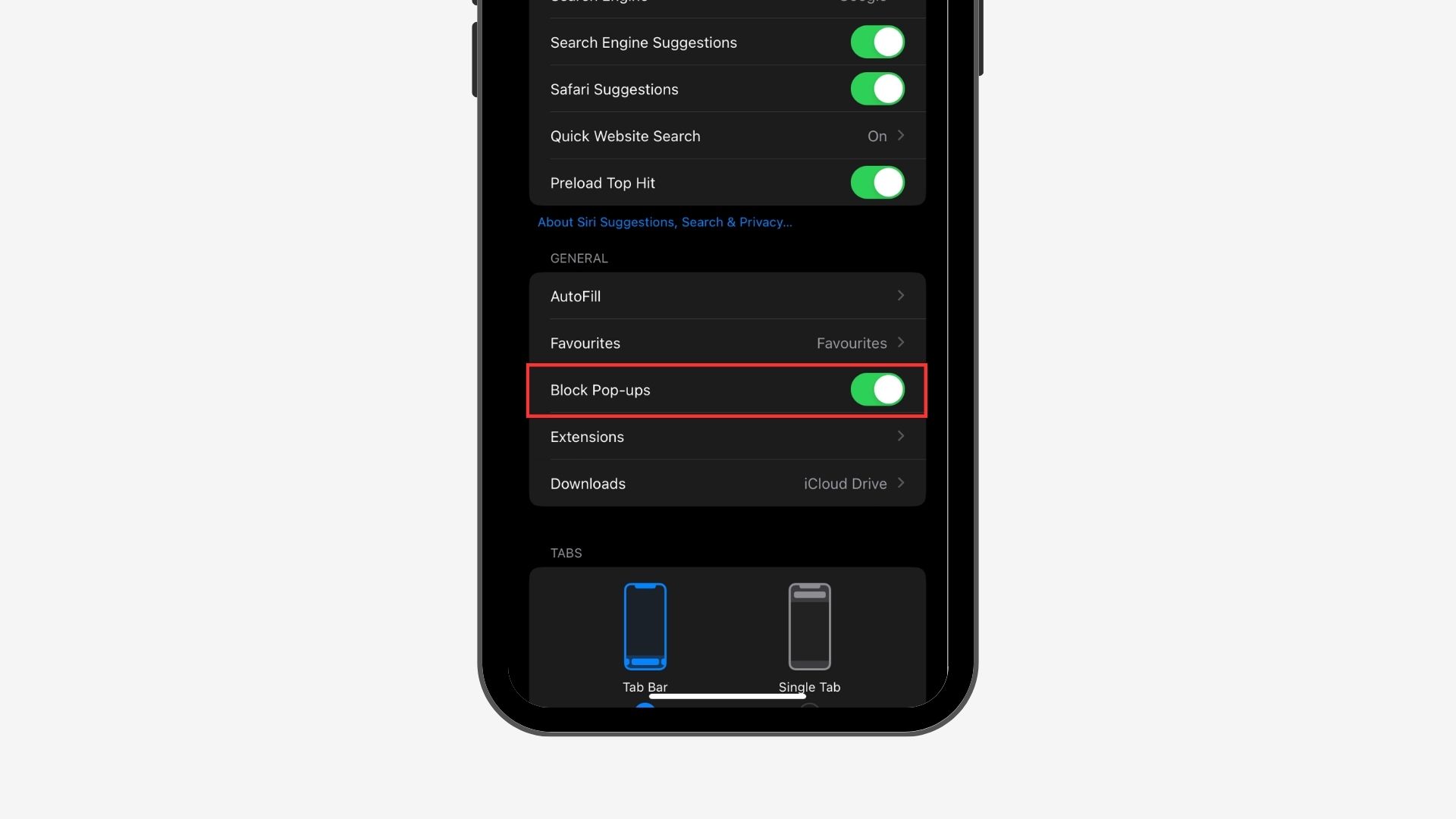
To ensure our safety while browsing potentially hazardous websites, we should disable pop-ups. Clicking on a pop-up by mistake could result in a security breach.
- Go to Settings, then look for Safari.
- Find “Block Pop-ups“
- Turn on the toggle if it’s off.
8. Turn on “Prevent Cross-Site Tracking”
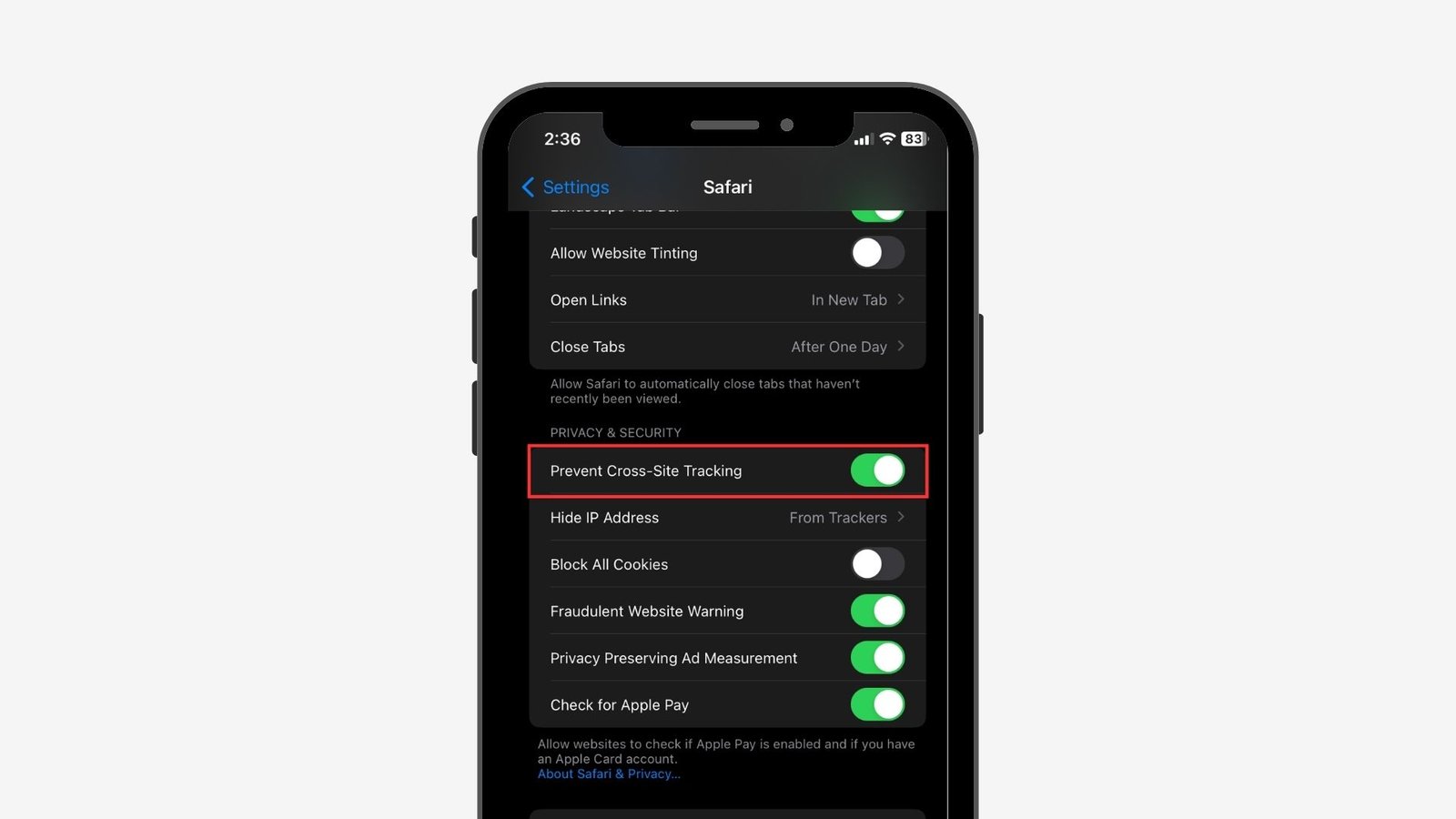
Enabling the setting will prevent new web pages from accessing previously closed ones, thereby ensuring secure browsing.
- Open Settings, and go to Safari.
- Scroll Down and Turn on “Prevent Cross-Site Tracking“
9. Turn on “Fraudulent Website Warning”
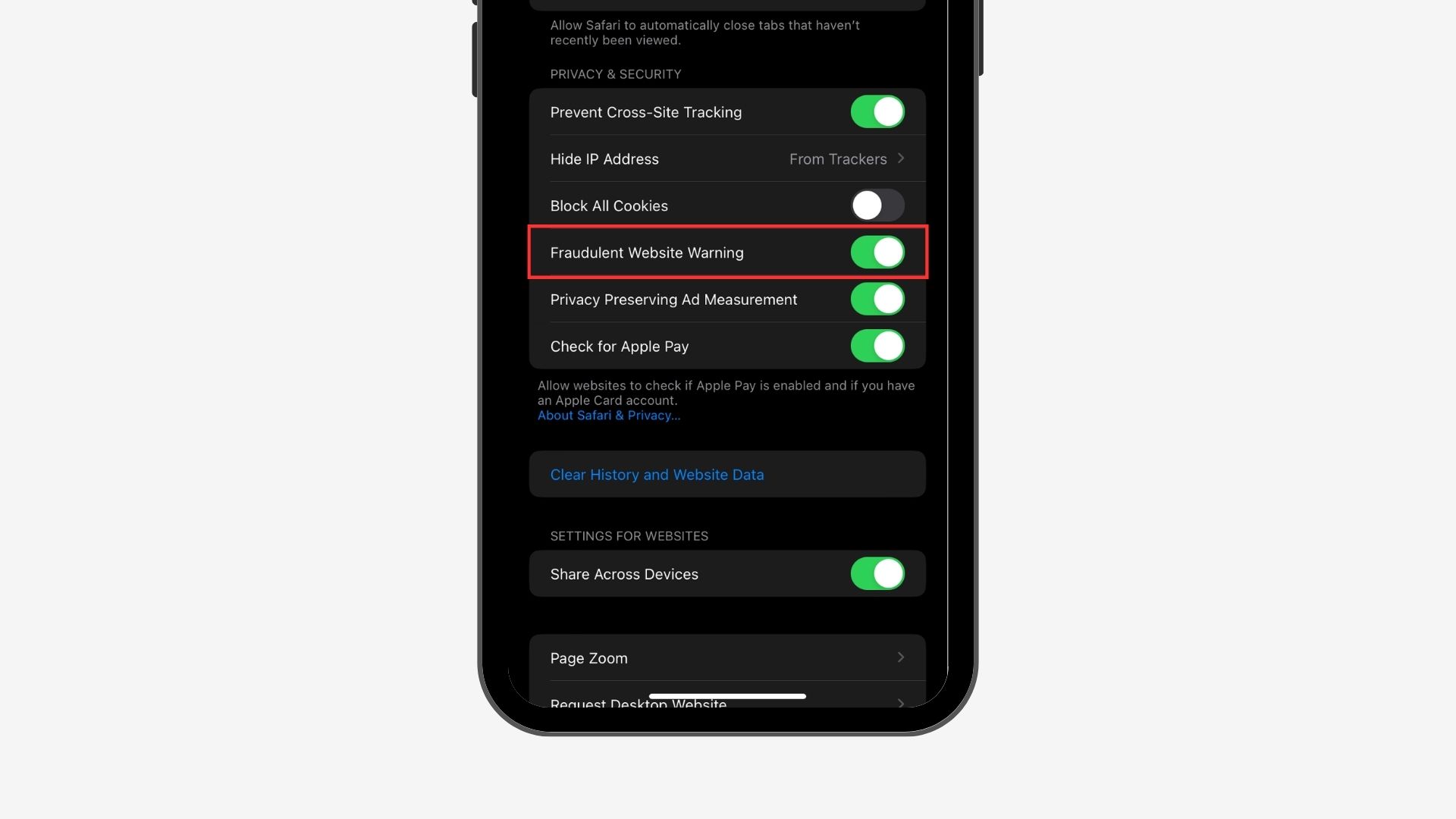
The iPhone will issue a warning if it detects that the website you’re about to visit is fraud.
- Again, Go to Settings and then Safari.
- And Turn on “Fraudulent Website Warning”
10. Security Recommendations
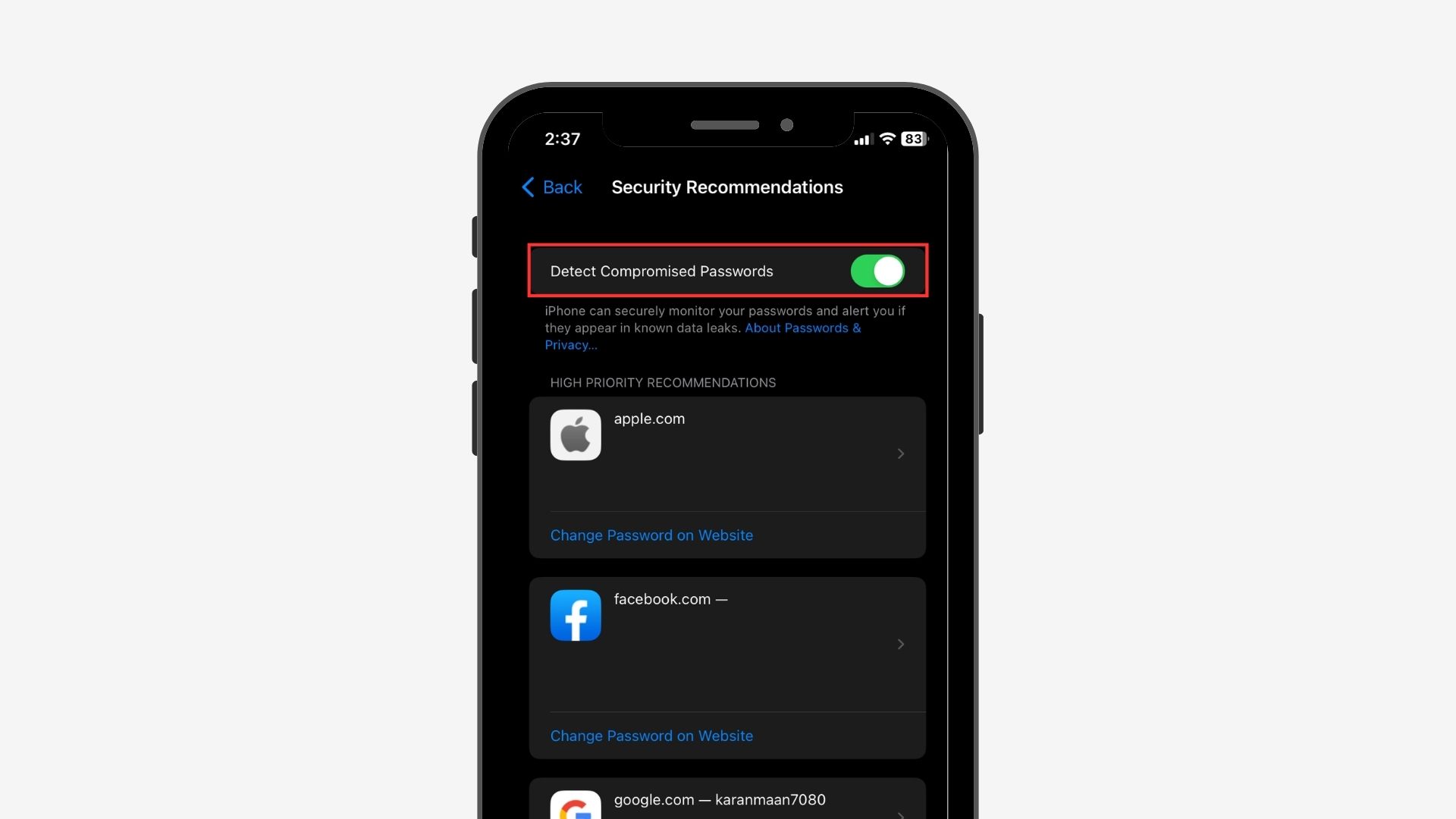
After all the safari settings are changed, follow the below steps for more protection.
- Go to Settings and then click on Passwords.
- There you will find Security Recommendations.
- Toggle on “Detect compromised passwords“
By scrolling down, you can access high-priority recommendations that identify reused or compromised passwords. Many of us tend to reuse passwords across multiple websites, often out of a reluctance to remember multiple passwords. This feature is therefore an essential tool for improving our online security.
It’s important to review the list carefully to identify any passwords that may have been involved in a data breach or are being reused. By doing so, you can take appropriate measures to ensure your online safety.
11. 2-Factor Authentication
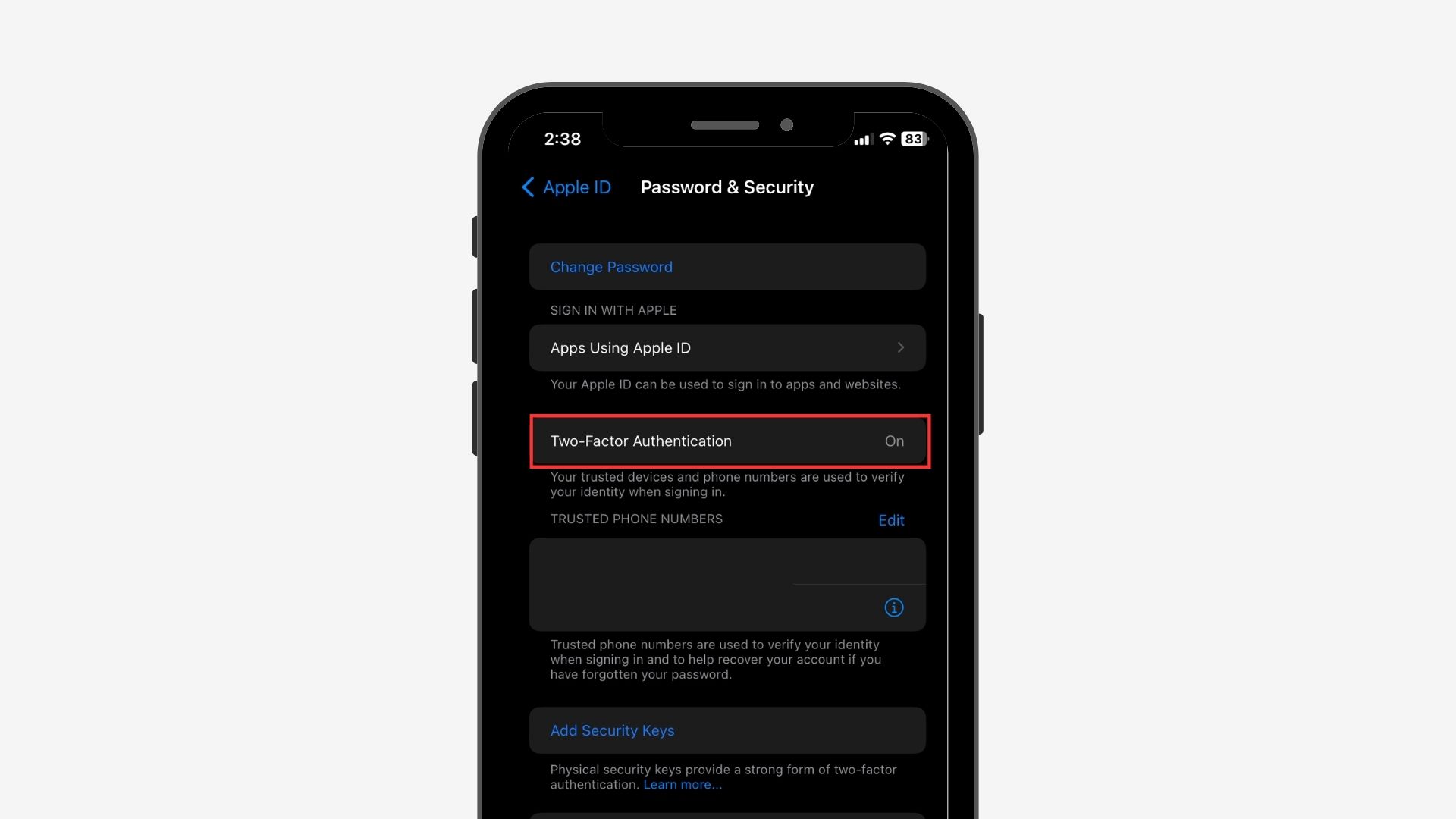
Your reliable devices serve the purpose of confirming your identity, and in case you forget your password, they can aid in retrieving access to your account.
- Go into Settings → Your Apple ID → Password & Security
- Turn on “2-Factor Authentication“